Securing the microelectronics supply chain
Advancing microelectronics security through innovative research
The good news about microelectronics challenges, Kinsy says, is that new technologies and techniques are being developed to improve security and trust.
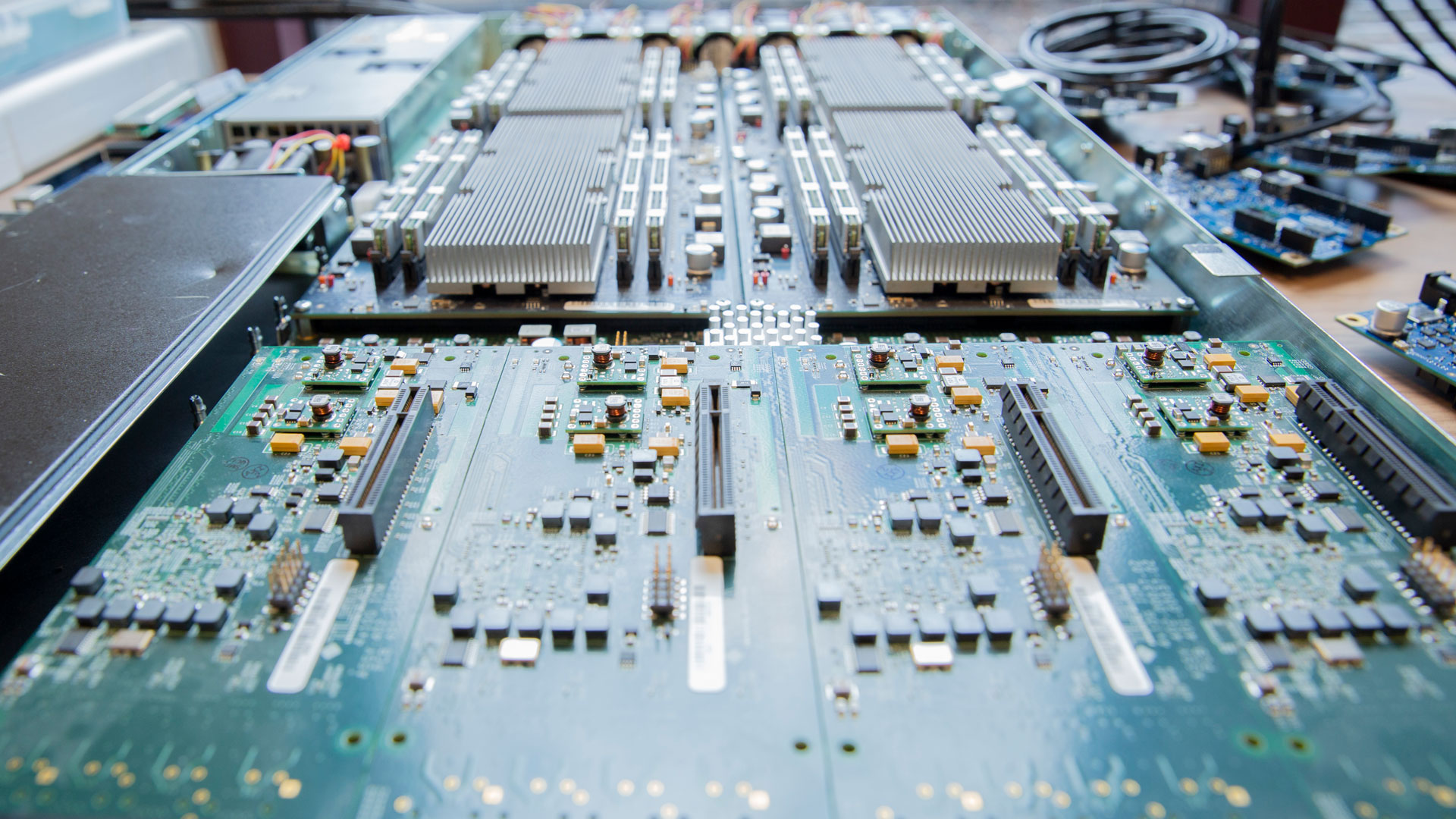
Agencies like the US Department of Defense adopt “zero trust” policies, which assume that no microelectronics are secure and that everything must be validated. Validation can take the form of using advanced imaging technologies and forensic methods to detect counterfeits and malicious circuitry. Components can be marked or tagged to authenticate and track supply chain movement. Additional technologies can be applied to prevent exploitation and counter security threats.
The role of the STAM center in advancing microelectronics security is to study emerging microelectronics technologies, new computational paradigms, and new secure root-of-trust hardware techniques through research and development.
The center adopts a very integrated approach to its organization with two technological laboratories and four application laboratories.
The two technological laboratories focus on the development of new components for microelectronics. The Semiconductor Security Laboratory, or SemiSec, focuses on the design of low-level secure integrated circuits, or ICs, while the Laboratory for Unconventional Computing Substrates, or LUCS, studies emerging substrates and post-processing technologies. -CMOS. CMOS, or complementary metal-oxide-semiconductor, is the main underlying design of modern integrated circuits.
Application labs take new components developed in technology labs to develop new computer systems. The Adaptive and Secure Computing Systems Laboratory, or ASCS, develops adaptive and self-healing secure computing systems. The Artificial Intelligence Technology and Systems Lab examines secure and privacy-preserving AI/ML systems. The Computer and Embedded Systems Architecture Laboratory designs secure and high-performance computer architectures. The Secure and Resilient Cyber-Physical Systems Laboratory focuses on the deployment of microelectronics in critical infrastructures.
Each lab’s focus area is intended to complement the others in designing and prototyping complete, secure and reliable, application-focused systems that demonstrate real-world impact. The projects cover several laboratories and integrate the resources of each and the expertise of their researchers.
“This strategic approach provides the center with a strong differentiator and enables a faster path to market,” says Kinsy.
STAM Center researchers are exploring IC security through vertically stacked ICs in a technique called 3D integration. They are also exploring forgery-resistant and anti-cloning design methodologies, as well as other design obfuscation and masking techniques that use self-adaptation to automatically respond to threats.
Using artificial intelligence and machine learning applications, researchers are developing defenses against hardware and intellectual property theft.
Research teams are also developing reliable circuit analysis tools with hardware-in-the-loop simulation capabilities and techniques to keep data and identities private.
Other projects focus on developing a cost-effective approach to comprehensively test the performance of electronic components in the final product.
The work of the STAM Center continues to evolve to meet emerging real-world challenges in microelectronics security. With the rise in counterfeit threats during the pandemic, researchers’ work has accelerated in this area.
“We were able to collect more chips and identify new counterfeiting techniques,” Kinsy says.
Train the next generation of microelectronics professionals
Kinsy earned a bachelor’s degree in computer science and computer systems engineering from ASU nearly 15 years ago and returned to the university as a faculty member in 2021.
“A constant thought I have about ASU’s computer systems engineering program over the years is how well it prepared me,” says Kinsy. “It is very impressive to see how ASU has continued to transform and grow since my undergraduate years. It is a great joy to be able to add to that. As a faculty member, I would like to strengthen the computer systems engineering graduate program with more emphasis on hardware and microelectronics security.
Beyond the curriculum at Fulton Schools, Kinsy wants the STAM Center to help build the local workforce to keep and attract semiconductor companies to the Phoenix area.
“Without a strong, highly skilled workforce, the semiconductor industry doesn’t take root,” he says. “Just 20 years ago, the United States manufactured 40% of the world’s microchips. Today we are down to about 11%. This erosion reflects the trend of investments in education.
Kinsy helps develop an exposure and outreach pipeline program of Saturday electronic design workshops, seminars, webinars, short and long-term professional development training courses, and a certification process. Collaboration with local semiconductor companies includes regular industry open houses, research and development partnerships, and internship and student placement programs.
Recently, the STAM Center launched the Arizona Cyber Range, or AzCR, a training platform for hardware/electronic device security issues. Trainees will have access to microcontrollers, industrial control systems, Internet of Things devices and more, and can explore the systems through virtual environments to learn valuable skills.
“Our short-term goal is to serve the local Phoenix microelectronics industry and use our local success to establish a national position for the creation of a sustainable research training program in secure and reliable microelectronics,” said said Kinsy.
“Phoenix is the perfect environment to ensure that the STAM Center’s research, education and outreach efforts reflect the makeup of the entire American population,” he said. “We want to serve as a national model for recruiting, engaging, and training non-traditional students and veterans of the U.S. Army, especially those from underrepresented groups and underserved communities.”
Comments are closed.