Chinese cyber spies target governments with their ‘most advanced’ backdoor
Security researchers have discovered Daxin, a China-linked stealth backdoor specifically designed for deployment in hardened corporate networks with advanced threat detection capabilities.
According to a technical report released today by Symantec’s Threat Hunter team, Daxin is one of the most advanced backdoors ever deployed by Chinese actors.
A point of differentiation from Daxin is its form, which is a Windows kernel driver, an atypical choice in the malware landscape. Its stealth comes from its advanced communication features, which mix its data exchanges with regular internet traffic.
“Daxin is, without a doubt, the most advanced malware that Symantec researchers have seen used by a China-linked actor,” Symantec said in a new report.
“Given its capabilities and the nature of its deployed attacks, Daxin appears to be optimized for use against hardened targets, allowing attackers to dig deep into a target’s network and exfiltrate data without arousing suspicion. .”
Hide in legitimate network traffic
Backdoors provide hackers with remote access to a compromised computer system, allowing them to steal data, run commands, or download and install other malware.
Since these tools are typically used to steal information from protected networks or further compromise a device, they must involve some form of encryption or obfuscation of the data transfer to avoid raising alarms on network monitoring tools. network traffic.
Daxin does this by monitoring network traffic on a device for specific patterns. Once these patterns are detected, it will hijack the legitimate TCP connection and use it to communicate with the command and control server.
By hijacking TCP communications, Daxin malware can hide malicious communications in what is perceived to be legitimate traffic and thus remain undetected.
“Daxin’s use of hacked TCP connections provides a high degree of stealth to its communications and helps establish connectivity across networks with strict firewall rules. It may also reduce the risk of discovery by SOC analysts. monitoring network anomalies,” the Symantec report explained. .
This essentially opens up an encrypted communication channel to transmit or steal data, all through a seemingly harmless TCP tunnel.
“Daxin’s built-in functionality can be increased by deploying additional components on the infected computer. Daxin provides a dedicated communication mechanism for these components by implementing a device named .Tcp4,” Symantec explained.
“Malicious components can open this device to register for communication. Each of the components can associate a 32-bit service identifier with the opened .Tcp4 handle. The remote attacker is then able to communicate with selected components by specifying a corresponding service identified when sending messages of a certain type.
Daxin is also notable for its ability to establish complex communication paths across multiple infected computers at once, using a single command to a set of nodes.
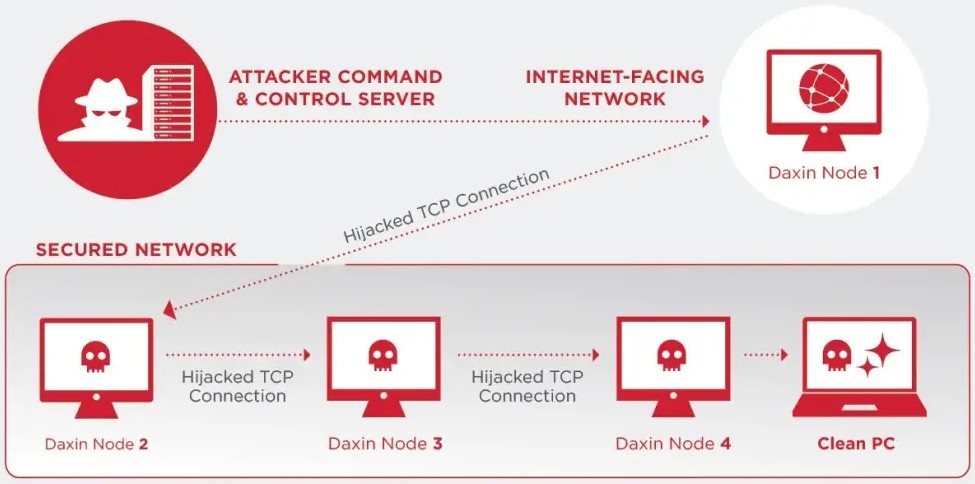
This allows threat actors to quickly re-establish encrypted connections and communication channels in well-protected networks.
At the same time, as long as the nodes are active and serve as relay points, the chances of malicious traffic being flagged as suspicious are minimized.
Chinese cyber espionage
Symantec threat analysts have found evidence linking Daxin to the Chinese state-backed Slug (aka Owlproxy) hacking group.
Reportedly, the particular backdoor has been actively used in attacks since at least November 2019, while researchers again spotted signs of its deployment in May 2020 and July 2020.
The most recent attacks involving Daxin were seen in November 2021, targeting telecommunications, transportation, and manufacturing companies.
It should be noted that Symantec claims the malware was first sampled in 2013, already exhibiting the advanced detection and avoidance techniques we see in the current version.
However, no attacks involving Daxin were observed until later, although it is likely that stealth hackers simply remained undetected until 2019.

Comments are closed.